Difference Between Nmap and Masscan
The enumeration of hosts is one of the first things you probably do while doing information gathering of a penetration test. What you basically do is make active connections to the target hosts and try to collect as much data as you can using queries in order to identify potential attack vectors in the system. While host enumeration is performed both internally and externally, it’s done with the help of a tool such as Nmap and Masscan. However, there are vulnerability scanners that can also do this as part of the automated testing. But, we are going to take a good look at Nmap and Masscan and try to understand their differences.

Nmap
Network Mapper (Nmap) is one of the most common and widely used tools for network reconnaissance. It’s used in the engagement of penetration testing and is the security auditing in cybersecurity. It’s a free, open source tool for network discovery used to discover hosts and services on a computer network. Nmap is a must-have tool for ethical hackers and it’s available on all platforms. It’s specifically designed to analyze massive networks as well as single hosts. This tool was originally developed by Gordon Lyon, infamously known as “Fyodor.” While there are other port scanners used for high speed scanning, Nmap is probably the only one with a scripting engine built into it. Nmap is still the de facto tool for network scanning in the information security industry.

Masscan
Masscan is yet another popular port scanner that has been developed to very large network scans very quickly. While Nmap can do scanning of large address blocks, it was not exclusively designed keeping that function in mind. Just like Nmap, Masscan is an open source internet-scale port scanner but is known for its high speed capacity, capable of scanning the entire IPv4 internet in under five minutes and transmitting 10 million packets in a second, all from just a single machine. In fact, it was developed solely for that purpose – to scan the entire internet as fast as possible. It’s useful for large scale surveys of the internet or of internal networks. This however requires adequate hardware and network bandwidth.
Difference between Nmap and Masscan
Functionality
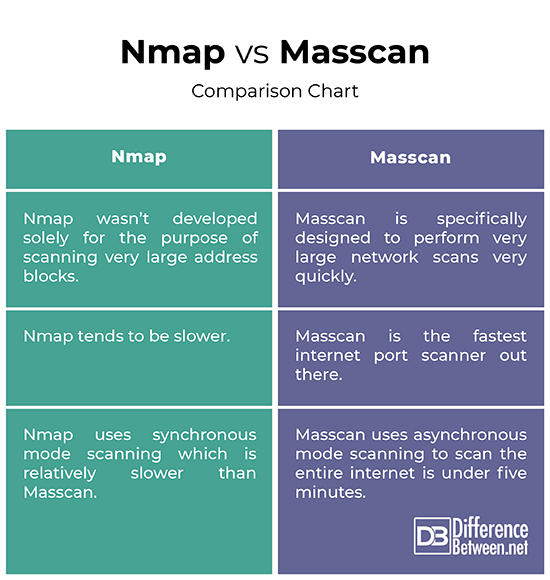
– While both Nmap and Masscan are the two most popular port scanners for network scanning and reconnaissance and security auditing, Masscan is tool specifically designed to perform very large network scans very quickly. Although, Nmap is still the de facto tool for network scanning, which obviously sets this tool apart from others, it wasn’t developed solely for the purpose of scanning very large address blocks. It isn’t very well optimized to do large scale scanning.
Speed
– Both Nmap and Masscan are free, open source tools for network discovery and produce basically the same results. However, Masscan is a really fast internet-scale port scanner that uses asynchronous mode scanning to deliver results much faster than with Nmap. In fact, it won’t be wrong to say that Masscan is the fastest internet port scanner out there, capable enough to scan the entire IPv4 internet in just five minutes or so, transmitting about 10 millions packets in a second, from a single machine.
Communication Mode
– Port scanners can be classified either as synchronous or asynchronous which basically measures their scanning capabilities. Masscan uses asynchronous mode scanning to scan the entire internet is under five minutes, give or take. As a TCP port scanner, Masscan sends a message and rather than waiting for a host’s response, it keeps sending while creating separate threads for each port. This ability makes it transmit at high rates of speed. Nmap, on the other hand, uses synchronous communication and waits for the host’s response to determine if the port is alive. Thus, synchronous scanners like Nmap are slower.
Nmap vs. Masscan: Comparison Chart
Summary
When it comes to information security, Nmap is still the de facto standard for network scanning and security auditing. It enables you to scan your network and lets you determine what and who are connected to it, along with all the information about what’s connected and the services each host is operation, and so on. But, Nmap isn’t the only port scanner to do that. There’s Masscan, which is a fast and reliable network reconnaissance tool specially designed to perform very large network scans very quickly.
Does Masscan use Nmap?
Masscan is a network port scanner, operates in many ways similar to Nmap. But Masscan is really fast, thanks to its high speed capacity and asynchronous mode scanning technique.
What is Masscan used for?
Masscan is much like Nmap but is specifically developed to do very large network scans very quickly. It uses the same sorts of command-line parameters as Nmap. It is uses to enumerate a large number of hosts.
Is there anything better than Nmap?
There are quite a few tools that can be used to monitor networks like Angry IP Scanner, Dipiscan, ZMap Project, Masscan, and so on.
What is the difference between Nmap and Nessus?
Nmap is basically an open source port scanner that is used to scan the networks to gather information about the open ports. Nessus is a vulnerability scanner mainly used to identify and assess security vulnerabilities in an IT infrastructure.
Is Masscan better than Nmap?
is a fast and reliable network reconnaissance tool specially designed to perform very large network scans very quickly. But, Nmap also has some features and functionalities that are exclusive to Nmap. Also, Nmap is the de facto network scanning tool.
What is an advantage of using Masscan over Nmap?
One of the major advantages of using Masscan is that it’s capable of large scale surveys of the internet or of internal networks and is really fast. Masscan also uses asynchronous mode to scan the internet which makes it very efficient.
What is Nmap equivalent for Windows?
Angry IP Scanner is probably the best alternative to the Nmap port scanner and is able to scan ports and IP addresses very quickly.
How do I run Masscan on Windows?
The repository of Masscan can be found on https://github.com/robertdavidgraham/masscan. For Windows, use the VS10 project and use MinGW and type in ‘make.’
- Difference Between Caucus and Primary - June 18, 2024
- Difference Between PPO and POS - May 30, 2024
- Difference Between RFID and NFC - May 28, 2024
Search DifferenceBetween.net :
Leave a Response
References :
[0]Messier, Ric. Penetration Testing Basics: A Quick-Start Guide to Breaking into Systems. New York, United States: Apress, 2016. Print
[1]Calderon, Paulino. Nmap Network Exploration and Security Auditing Cookbook - Third Edition: Network Discovery and Security Scanning at Your Fingertips. Birmingham, United Kingdom: Packt Publishing, 2021. Print
[2]Messier, Ric. CEH v10 Certified Ethical Hacker Study Guide. New Jersey, United States: John Wiley & Sons, 2019. Print
