Difference Between Phishing and Pharming
The harsh reality of this digital age is that we are far more likely to become a victim of cyber crime than a physical crime. Many people are familiar with the term crime, but a few understand the concept of cyber crime. Cyber crime in many things and fraud is one of financially motivated cyber crimes that have migrated online. It’s surprising to think that someone with a little knowledge can gain so much information about you and about your online behavior just by reviewing your emails. However, the reality is it’s possible. There are many opportunities for cyber criminals to sneak into your computer and network. Cyberspace gives cyber criminals the opportunity to target victims regardless of their location.
Phishing is one common type of fraud which is a growing problem on the internet. Phishing is a scam in which an attacker attempts to commit identity theft, luring victims into providing personal or confidential information such as social security numbers, credit card numbers, bank account numbers, ATM PINs, etc. Simply put, phishing is stealing someone’s identity online. Pharming is yet another major security threat that seeks to obtain personal, private and financial information of users through domain spoofing. Pharming is fast emerging as one of the most dangerous Internet scams specifically designed to poison a DNS server.
What is Phishing?
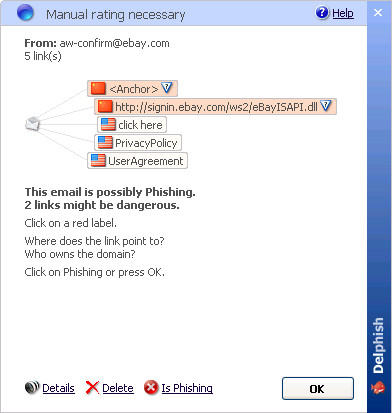
Phishing is one of the common Internet scams in which an attacker attempts to trick the victims into providing confidential information such as passwords, bank account numbers, credit card details, ATM PINs, social security numbers, etc. Phishing is a big scam run by potential hackers via email or instant message. In a standard phishing attack, a victim receives a fraudulent email or message that appears to be from a legitimate source such as a bank or any other financial institution, and which might contain a link to a website seeking personal details from users. The message or email usually indicates a desperate need to update an account immediately urging users to click on them without verifying the source. Phishing targets all kinds of personal information, including user names and passwords, bank account numbers and credit card details, and more.
What is Pharming?
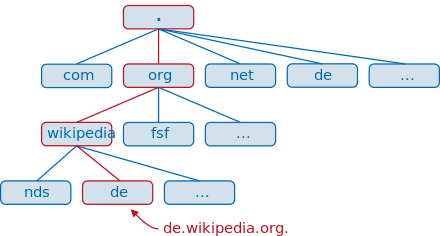
Pharming is yet another Internet scam which is similar in nature to email phishing except it seeks to obtain personal or private financial-related information through domain spoofing. Unlike phishing, pharming uses domain spoofing rather than using messages or emails to trick victims into visiting malicious websites that appear legitimate. Pharming exploits the design and implementation flaws in Domain Name System (DNS) services and the way Internet addresses are resolved to Internet protocol addresses. It simply manipulates components of the domain and host naming system, redirecting user from one website to another. When a victim enters the poisoned server’s web address, he or she is simply navigating to the attacker’s website. Because the victim sees the correct web site on the address bar, it makes pharming difficult to detect.
Difference between Phishing and Pharming
-
Definition of Phishing vs. Pharming
– Phishing is one of the common Internet scams in which an attacker attempts to trick the victims into providing confidential information such as passwords, bank account numbers, credit card details, ATM PINs, social security numbers, etc. Pharming is yet another Internet scam which is similar in nature to email phishing except it seeks to obtain personal or private financial-related information through domain spoofing. Pharming simply manipulates components of the domain and host naming system, redirecting user from one website to another.
-
Target of Phishing vs. Pharming
Phishing attack is an attempt to scam people one at a time via an email or instant message and it targets all kinds of personal information, including user names and passwords, date of birth, bank account numbers and credit card details, and social security numbers.
Pharming, on the other hand, allows scammers or attackers to target large groups of people at one time through domain spoofing rather than using messages or emails to trick victims into visiting malicious websites that appear legitimate. Pharming simply redirects traffic from one website to a different, identical-looking website.
-
Nature of Phishing vs. Pharming
Pharming is similar to nature to email phishing as it equally seeks to obtain personal and private financial-related information from users through domain poisoning. Pharming is more dangerous, since users are redirected to a fake website which is an exact replica of the original website, without any prior knowledge or participation on their part. In addition, pharming is more difficult to accomplish and identify because a successful pharming attack leaves no trails on the user’s computer to indicate that anything is wrong with the system.
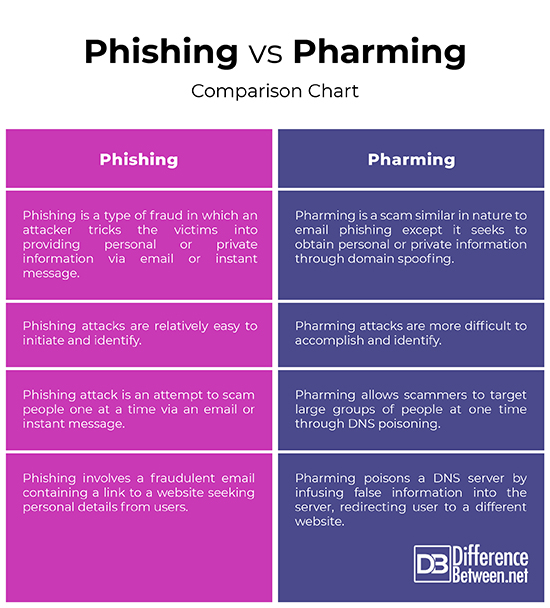
Phishing vs. Pharming: Comparison Chart
Summary of Phishing verses Pharming
While both phishing and pharming are the two different ways hackers trick victims into providing confidential or financial-related information via the Internet, they differ a lot from each other. Phishing is simply sending the victim a fake email asking him to share his personal or confidential information such as date of birth, bank account details, credit card numbers, ATM PINs, and social security numbers. Pharming, on the other hand, involves poisoning the DNS of a website so that the user is redirected to an imposter website which is an exact replica of the original website. This is probably why pharming is more insidious than phishing as it manipulates information up to the DNS level making it more difficult to identify.
- Difference Between Caucus and Primary - June 18, 2024
- Difference Between PPO and POS - May 30, 2024
- Difference Between RFID and NFC - May 28, 2024
Search DifferenceBetween.net :
1 Comment
Leave a Response
References :
[0]Image credit: https://de.wikipedia.org/wiki/Domain_Name_System#/media/File:Dns-raum.svg
[1]Image credit: https://en.wikipedia.org/wiki/Delphish#/media/File:Delphish_possible_phishing.jpg
[2]Quigley, Marian. Encyclopedia of Information Ethics and Security. Hershey, Pennsylvania: IGI Global, 2007. Print
[3]Kim, David and Michael G. Solomon. Fundamentals of Information Systems Security. Burlington, Massachusetts: Jones & Bartlett Learning, 2010. Print
[4]Newman, Robert. Computer Security: Protecting Digital Resources. Burlington, Massachusetts: Jones & Bartlett Learning, 2009. Print

Pharming is a lot harder to pull off with modern technologies like DNSSEC. Perhaps Phishing and its cousin Pharting are what we should focus our efforts at preventing now.