The Difference between DOS and DDOS attacks
Denial of service (DOS) and distributed denial of service (DDOS) attacks are tools used by hackers to disrupt online services. The implications of these attacks can be wild – sometimes costing bigger companies millions of dollars.
If you run a business that is potentially a target for one of these attacks, or if you’re just interested in the subject, read on for ways to defend yourself from these types of attacks.
DOS Attacks
A DOS attack is an attempt to overload an online service (website) with traffic. The goal is to disrupt the website or network in order to stop legitimate users from accessing the service.
The DOS attack is usually launched from a single machine, as opposed to a DDOS attack which is launched from multiple machines.
Here’s a good metaphor.
Picture a shopping center where a recent incident has animal activists up in arms. These animal activists (illegitimate traffic) crowd the entrance to block shoppers (legitimate traffic) from entering the premises.
The shoppers can’t get to the stores and the stores lose money.
This is pretty much what a DOS attack is like, metaphorically speaking.
DDOS Attacks
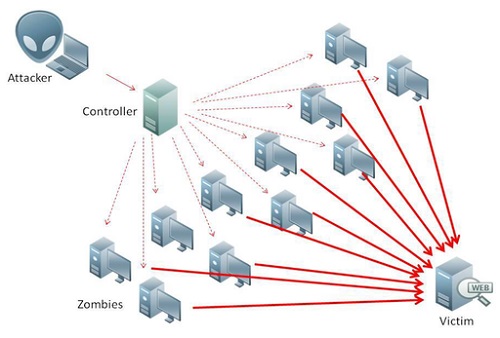
DDOS attacks are normally worse than DOS attacks. They are launched from multiple computers. The machines involved could number hundreds of thousands or more.
These machines aren’t all owned by the attacker, naturally. These machines are usually added to the hacker’s network by means of malware. This group of machines is also known as a botnet.
A DDOS attack is particularly frustrating to defend against, because it’s very difficult to tell legitimate traffic from attacker traffic.
There are many different DDOS attacks, such as HTTP or SYN flooding.
HTTP flooding is merely the practice of sending thousands upon thousands of requests to the server in an attempt to overwhelm it.
The SYN flood fills the TCP network with unacknowledged packets of data. This can have dire consequences and can even impact users unrelated to the intended victim.
Why would they attack me?
There can be many motivations for these types of attacks. It could be that corporations are at war and waging it on the web. It could be that someone seeks revenge for something. Or, as in our shopping center example above, it could be orchestrated by activists. Also called “hacktivists”.
Some criminals have even extorted money from businesses with this method. Just like a modern-day, technology-fuelled mafia.
What are the costs?
Cost implications from DOS and DDOS attacks can vary wildly. Attacks to some companies could cost a few dollars, and others could lose millions. Smaller companies may feel the losses worse than larger companies, however.
The far scarier cost is the potential damage they could do to your clients.
Some DOS and DDOS attacks can be distractions to cover up a breach attempt. Should this be the case and the breach is successful, thousands of clients’ personal info could be at risk.
Just take a look at the PlayStation Network’s debacle in 2011.
Who is at risk?
Everyone. No one is safe from a DOS or DDOS attack. In 2010, EA, Twitter and the PlayStation Network (among others) felt the brunt of a country-wide DDOS attack. Millions were lost. Also, with companies as big as these being targeted, what hope do the little fish have?
It’s best, then, to know how to stop one of these attacks should they come your way…
How do I protect myself?
Protecting against DOS attacks can be pretty simple. Victims can block the attacker’s IP address at firewall or ISP level, depending on the severity of the attack.
Security tools and enterprise products exist which can block ICMP or SYN attacks.
DDOS attacks are far harder to guard against, and there are various methods. One of these involve having the ISP trash all incoming traffic to the webserver, legitimate or not. This can help save and secure you client’s personal information.
Other ways are to use SYN cookies or HTTP reverse proxies, depending on the type of attack.
How can I help?
If you’re an individual who is irked by the fact that your pc may be on a hacker’s botnet, you’ll be happy to know there is a cure.
Any good antivirus can keep your pc clean from any and all malware. Every now and then you could meet something particularly nasty, and then it would just be a matter of reporting it to your anti-virus company, but mostly the next update will take care of nasty like these.
If you can afford to run multiple anti-virus programs, that’s even better.
Some malware are so sneaky, they pop into the back door and disable your anti-virus software. These types of viruses can even infect modems (from personal experience), so be careful.
A final note on DDOS
DDOS attacks happen literally every day. If you have assets online and fear a DDOS attack, the best thing you can do it contact a web-security expert. They may be pricey, and the software you need could be even more expensive, but you never know when you might need protection.
As they say, prevention is better than cure.
Summary
| DOS | DDOS |
| Attack launched by a single machine. | Attack launched by many machines, also called a botnet. |
| Can be stopped relatively easily with the right security. | Can be a real headache to prevent. |
| Low threat level, as these will rarely be used to cover a breach attempt. | Medium to high threat level, as these can be used to do some serious damage to networks and even systems. |
| No malware involved. | A botnet is usually made up of thousands of infected pc’s. |
- The Difference between Trello and Evernote - July 13, 2017
- Difference between iCloud Drive and Dropbox - July 13, 2017
- Difference between Garmin Vivofit 2 and Fitbit Charge - July 13, 2017
Search DifferenceBetween.net :
Leave a Response
References :
[0]https://www.us-cert.gov/ncas/tips/ST04-015
[1]http://www.networkworld.com/article/2170051/security/tech-primers-four-ways-to-defend-against-ddos-attacks.html
[2]http://www.esecurityplanet.com/network-security/how-to-prevent-dos-attacks.html
[3]https://commons.wikimedia.org/wiki/File:Ddos-attack-ex.png